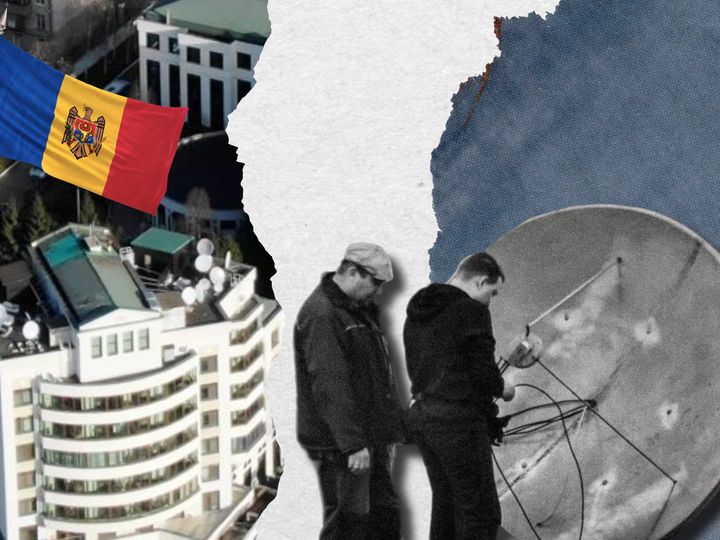
Year after year, the number of dishes and transmitting devices on the rooftop of the Russian embassy in Chisinau keeps growing, accompanied by the regular appearance of enigmatic figures. This rooftop activity becomes particularly noticeable ahead of presidential or parliamentary elections, as well as during the visits of foreign delegations to Moldova. Notably, such activity occurred before the June 1 Eurosummit and in May following a cyber-attack on government networks, which resulted in thousands of classified documents being compromised. Jurnal TV (Moldova) and The Insider managed to identify the individuals on the embassy rooftop: they turned out to be covert communication officers associated with the GRU and SVR, closely connected to hacker groups responsible for breaching the electronic mailboxes of Angela Merkel, Emmanuel Macron, and Hillary Clinton.
People on the rooftop
On May 14, 2023, at approximately 1:30pm, while most of the city's residents were enjoying their weekend at their country retreats, a balding man made his way to the rooftop of a residential building within the premises of the Russian embassy in Chisinau. With a vigilant look around, he proceeded to set up and manipulate transmitting parabolic antennas, and carefully handle the connecting cables. This man was identified as Pavel Yakunin, originally from Ryazan. Prior to his service in the GRU, he had completed his studies at the Cherepovets Military Institute of Radio Electronics. Within the embassy, Yakunin holds a discreet role as an officer in the military attaché system, and only a select few are aware that he is responsible for overseeing the secret communication channels connected to GRU headquarters in Moscow and the reception center for space intelligence in Vatutinki, near Moscow.
The motive behind Yakunin's rooftop visit on that particular Sunday remains a matter of speculation. It is conceivable that it could be linked to the upcoming Eurosummit and the recent cyber-attack on the internet resources of Moldova's President's administration, government, Ministry of Foreign Affairs, and the Information Technology and Cybersecurity Service (STISC). This breach resulted in the leakage of a substantial amount of classified correspondence involving high-ranking officials and certain law enforcement agencies, as well as other critical information. Additionally, on the same day, the Gagauzia region was holding elections for its head, and GRU supervisors were eagerly awaiting updates from their agents through a secure communication line. After spending about an hour on the rooftop, Yakunin discreetly disappeared back into the confines of the embassy.
Pavel Yakunin on the Embassy's rooftop
Since 2015, Russian intelligence has been displaying increased activity in Moldova, particularly after Moscow definitively backed socialist Igor Dodon, who went on to assume the presidency of the country a year later. As a staunch Kremlin ally, Dodon required support from friendly intelligence services, leading to an influx of personnel from the GRU (Main Intelligence Directorate), SVR (Foreign Intelligence Service), the 5th Service of the FSB (Federal Security Service), and employees of Moldova's Division of the Presidential Directorate for Interregional and Cultural Relations with Foreign Countries. The latter group consists predominantly of former intelligence agents.
According to information available to The Insider, individuals such as Sergey Sarapulov, Sergey Korolev, Igor Naumenko, Alexander Mironov, Konstantin Valday, Alexander Koshurenko, and Alexander Chikurov are known to have visited Moldova. These visitors are associated with the radio reconnaissance division of the GRU, and some of them specialize in phone surveillance and computer network hacking.
Sergey Korolev
For instance, Sergey Korolev, who visited Chisinau twice, had been engaged in spying while posing as a diplomat at the Russian Consulate in San Francisco. In 2016, he was exposed and subsequently expelled along with 34 other embassy personnel. Another “tourist,” Alexander Chikurov, serves in the 85th Main Special Service Center of the Ministry of Defense (Military Unit 26165), often referred to as the hacking division of the GRU. As revealed by The Insider in 2017, it was Military Unit 26165, located at 20 Komsomolsky Prospekt in Moscow, that operated under the codename APT28 (Fancy Bear). This group was responsible for hacking into the servers of the U.S. Democratic Party and the campaign staff of Hillary Clinton. Later, they also breached the email accounts of Emmanuel Macron's campaign team and German Bundestag deputies. In 2018, four officers from this unit were deported from the Netherlands after attempting to hack into the computer networks of the Organization for the Prohibition of Chemical Weapons.
Alexander Chikurov
In addition to eavesdroppers and hackers from military intelligence, 23 officers from the technical department of the SVR were observed on the embassy rooftop (the full list is available to The Insider). For example, Konstantin Gunin had previously worked at the FSB Scientific and Technical Center Atlas, which is now part of Rostech. Gleb Zhiltsov worked at the 3rd Research Institute of the Ministry of Defense, specializing in weapon development and military technology. Mikhail Yumashev studied at the Department of Information Management and Protection at the Russian University of Transport. Vladimir Korotkov transitioned to intelligence from the company SVEMEL, which “provides comprehensive information security services“ for Russian government institutions. Another visitor, Vladimir Skugarevsky, studied at the Faculty of Cybernetics at the Moscow State Technological University (MIREA), while Sergey Romanchikov graduated from the Bauman Moscow State Technical University. As for Evgeny Petrenko, he used to live in a house for special service personnel on Michurinsky Prospekt. Spotted among other Russians was also Taras Alexin from the Main Sanitary and Epidemiological Supervision Center of the Ministry of Defense. He did not appear on the rooftop and was likely dealing with rats that gnawed on the cables and wiring in the basement.
Rooftop installations
According to Moldovan journalists from Jurnal TV, they have noticed that as soon as a group of “tourists” arrives from Moscow, there's a flurry of activity on the rooftop of the Russian embassy. They have counted a total of 28 dishes, masts, transmitting, and receiving devices installed on the rooftops of both the embassy itself and the neighboring building where diplomats and technical personnel reside. Remarkably, this number far surpasses the record held by the Russian Embassy in Belgium, which boasts 17 antennas according to the Dossier Center portal. In comparison, the Russian embassy in Chisinau has 11 more antennas, making it stand out for its exceptionally high number of installed communication equipment.
The number of antennas on Russian embassy in Chisinau surpasses the record held by the Russian Embassy in Belgium
The majority of the dishes and antennas are located on the residential building adjacent to the embassy, playfully referred to by Russian diplomats as “our hotel.” On the rooftop of this building, one can find various types of equipment, including classic satellite dishes, yagi-uda arrays, magnetic loop antennas, and vertical masts.
According to experts, the parabolic antennas serve multiple purposes, such as establishing satellite communication, microwave relay links, or boosting the signal of wireless internet routers. Additionally, they can be utilized for locating ships, aircraft, and guided missiles. Parabolic antennas are also capable of intercepting signals from satellite telephony systems like Thuraya, enabling the interception of telephone conversations across numerous European countries.
Yagi-uda arrays are capable of intercepting radio conversations of local police, taxi drivers, air traffic controllers, and others. The broadband discone antennas with 360-degree radiation patterns are used for two-way communication within a line of sight of up to 100 km, allowing direct communication with the leadership of pro-Russian territories like Transnistria and Gagauzia. They are also used for short message exchanges with satellites in space, capable of transmitting large amounts of information within one second. Satellite discone antennas are installed at all Russian embassies worldwide and are utilized by the GRU, SVR, and the 5th Service of the FSB. Incidentally, in 2013, Putin's decree allowed the 5th Service to expand their staff at embassies, including specialists in recruitment, radio interception, external surveillance, and encryption.
Embassy technician Roman Romanenkov (left) and SVR officer Mikhail Yumashev (right)
The directional HF (High Frequency) antenna is used for both data transmission and reception at distances of 50-60 km. Within the HF range (from 3 to 30 MHz), it facilitates the transmission of voice messages and interception of signals in the HF frequencies. Its capabilities enable maintaining communication with ships of the Black Sea Fleet, or it can serve as a backup channel. Additionally, on the rooftops, there are UHF (Ultra-High Frequency) discone antennas for direction-finding, vertical masts for radio communication within Chisinau, and a microwave antenna used for suppressing GSM signals.
In December 2022, two officers from the 309th Central Radio Direction Finding Center of the GRU, Roman Yartsev and Sergey Gusev, were spotted on the embassy rooftop. They installed an MIMO (Multiple Input Multiple Output) antenna capable of transmitting information simultaneously through multiple channels.
It has been observed that GRU officers are responsible for the antennas on the right side of the residential building, while SVR officers take care of those on the left side.
Eavesdroppers and hackers
Every 2-3 years, there is a rotation of “eavesdroppers” and specialists in computer network hacking at the Russian embassy. Notably, the appearance of former Second Secretary Andrey Lenev on the embassy's rooftop resulted in a sharp increase in the number of transmitting and receiving devices. Lenev was accredited in Moldova from 2016 to 2019, and he is known as a “very skilled specialist in gathering information from state-owned fiber optic networks.” He graduated from the Military-Diplomatic Academy of the GRU (MDA), renowned for training professional spies. In 2011, he was dispatched as a vice-consul to San Francisco, where he spent nearly 5 years before arriving in Chisinau. The current whereabouts of this “diplomat” are unknown.

Andrey Lenev
At present, the officers in charge of communications and “listeners” in Chisinau are commanded by Alexander Vasinovich. He frequently appears on the embassy's rooftop, providing instructions to his subordinates. Vasinovich began his service in the GRU at the Kildinstroy settlement near Murmansk (Military Unit 34630), and later graduated from MDA. Prior to his assignment in Moldova, Vasinovich spied in Germany for several years. The spy's children shared numerous photos on social media from their time living in Berlin and traveling the world. Under Vasinovich's command are two other GRU officers: Vitaly Renev, a native of Riga, who has yet to pay a 500 ruble fine issued by the traffic police (GIBDD) back in 2016, and Pavel Yakunin, mentioned earlier, who was spotted on the rooftop before the Eurosummit.

Alexander Vasinovich on the Embassy's rooftop
On the SVR side, the embassy rooftop is frequented by attaché Vladimir Gorokhov, who previously served at the Kuznechiki settlement near Podolsk (Military Unit 43169), and Eduard Osechkin, a graduate of the Moscow Higher Command School of Road and Engineering Troops.
A source within Moldova's border service revealed that the wives of some of the aforementioned intelligence officers suspiciously travel to Moscow and back every 2-3 years. Most of the time, they carry 5-6 flash drives and hard disks in their hand luggage. “We believe that these women are being used as couriers to transport excessively 'heavy' files. Unfortunately, due to their diplomatic immunity, we are not authorized to conduct searches on them,” the source said.
The wives of intelligence officers are being used as couriers to transport excessively 'heavy' files
It should be noted that before the cyber-attack on the government's computer networks in Moldova, there was significant activity not only on the rooftops but also in central Chisinau. Cars would frequently depart from the embassy, making brief stops near government buildings, the parliament, and the Information and Security Service (analogous to the FSB and SVR). Passengers would carry small backpacks containing laptops and tablets. During these stops, the visitors communicated with someone via mobile phones before moving on to another location. Military attaché personnel or external counterintelligence officers from the SVR accompanied them during their trips.
Interviewed cybersecurity specialists speculated that the mysterious passengers in the cars were most likely members of the hacker groups APT28 or APT29, closely connected to Russian intelligence agencies. Hackers typically use Wi-Fi scanners to identify vulnerabilities in computer networks and deploy malicious viruses. Members of APT28 or APT29 have previously targeted various institutions, including the White House, foreign ministries of the Czech Republic, Poland, Germany, Italy, Latvia, Estonia, Ukraine, Norway, and the Netherlands, as well as the defense ministries of Denmark, Italy, and Germany, NATO headquarters, OSCE, IOC, WADA, and others. They have even managed to hack the email of Chancellor Angela Merkel of Germany and President Emmanuel Macron of France, as reported by The Insider earlier.
By the way, while this material was being prepared, an interview with the head of the cybersecurity department of Romania's intelligence service, Anton Rog, was released in neighboring Romania. The general reported that APT28 or APT29 attempted to hack government Wi-Fi networks, but the counterintelligence apprehended a local hacker who was working for Russian intelligence agencies.